Palo Alto Networks BPA+ Review
Partner Update

Written by: Scott Hammond, Senior Security Engineer
Connect with Scott on LinkedIn
Not long ago, our partner, Palo Alto Networks (PAN), announced its Best Practice Assessment Plus (BPA+) offering. This gives us the perfect opportunity to talk about it as well as their Security Lifecycle Review (SLR) tool. These tools are available from Palo Alto Networks to partners and customers for reviewing more than just configurations and applications present on the network. So let’s get to it.
What has your firewall done for you lately?
According to Gartner, “through 2023, 99% of firewall breaches will be caused by firewall misconfigurations, not firewall flaws.”
I know what you’re thinking. How do I know my firewall is misconfigured?
PAN has already made things easy for you with their BPA+. The best practice tool looks at the complexity of your existing configuration and compares your next-generation feature adoption rates with industry averages in your vertical. But what if you haven’t made your way over to team PAN yet? That’s where the SLR tool I mentioned comes in.
Security Life Cycle Review
The SLR that PAN offers is meant for both new and existing customers. It is a cyber threat assessment tool that gives customers visibility into real exposure of vulnerabilities, threats, and application usage, to better understand the risks organizations are facing (in real-time).
Some exciting things that the SLR will discover and report on are:
- Applications in use: Applications found in use present potential business and security challenges. As critical functions move beyond the control of internal IT, employees use non-work-related applications, or cyber attackers use them to deliver threats and steal data.
- High-risk applications: Applications that can introduce or hide malicious activity, exfiltrate data, or establish unauthorized communication.
- Software as a Service (SaaS) applications: Applications observed in the environment that your teams may or may not be managing.
- Vulnerability exploits: Total exploits observed in your organization, including protocol anomaly, code execution, etc.
- Total threats: Threats found on your network include vulnerability exploits, known and unknown malware, and outbound command and control activity.
- Malware detected: Known malware events observed in your organization.
The report generated will show all these metrics about industry averages, providing a baseline for your organization.
Nexum can arrange for an evaluation firewall to be sent to you. Upon receiving it, you will need to connect it via a Tap or SPAN port so that it can see all the happy little ones and zeros traversing your network. This can be a virtual firewall, as well.
That firewall will passively monitor for 7-30 days, after which time we export that data and run it through the SLR tool. We’ll provide you with the report, then discuss the findings with you, with possible next steps.
Already a PAN customer? We can work with you to set your existing firewalls to send data to Cortex Data Lake, where you can activate the SLR app in Cortex HUB and see an evolving insight into your Cyber Threat landscape.
Best Practice Assessment Plus
Where the SLR focuses on applications, vulnerabilities, and threats, the BPA tool is dedicated to analyzing your firewall configuration.
PAN often uses the race car and pit crew analogy to describe their firewalls. Your firewall was presumably configured with the current best practices at the time of installation by security professionals (not unlike me). The firewall is the race car here, and the security features are your pit crew. Now and again, it would be best if you pulled that firewall into the pit to fuel up and check the tires.
This is truly where PAN separates itself from other vendors who may tout “next-gen” capabilities. Just look at the size of this pit crew:
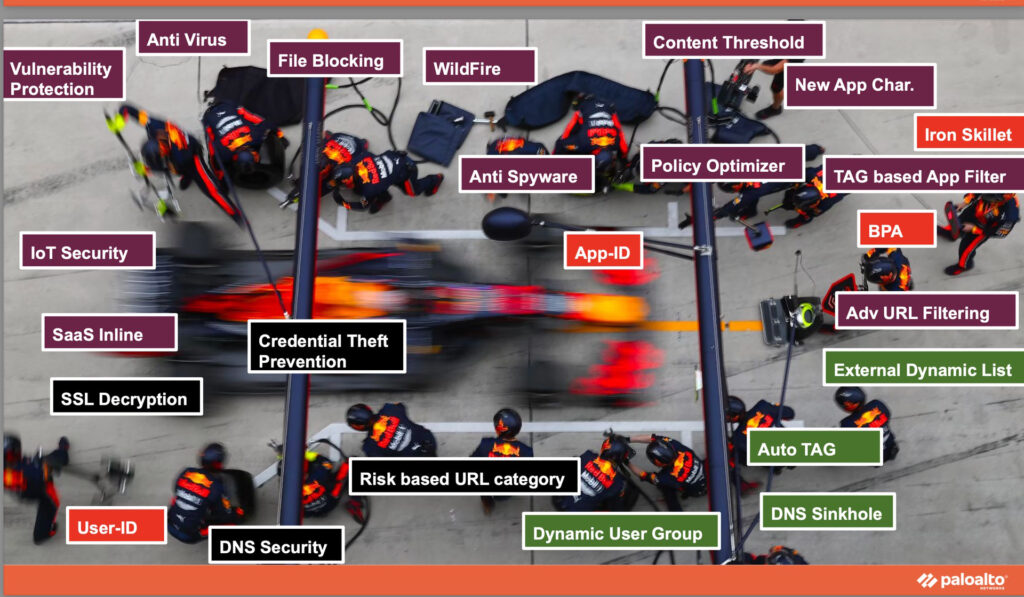 Vulnerability Protection, Anti-Virus, File Blocking, WildFire, Anti-Spyware, App-ID, Content Threshold, Policy Optimizer, New App Characteristics, Iron Skillet, TAG-based App Filter, BPA, Advanced URL Filtering, External Dynamic List, Auto TAG, DNS Sinkhole, Dynamic User Group, Risk-Based URL Category, DNS Security, Credential Theft Prevention, User-ID, SSL Decryption, SaaS Inline, IoT Security
Vulnerability Protection, Anti-Virus, File Blocking, WildFire, Anti-Spyware, App-ID, Content Threshold, Policy Optimizer, New App Characteristics, Iron Skillet, TAG-based App Filter, BPA, Advanced URL Filtering, External Dynamic List, Auto TAG, DNS Sinkhole, Dynamic User Group, Risk-Based URL Category, DNS Security, Credential Theft Prevention, User-ID, SSL Decryption, SaaS Inline, IoT Security
And that’s not even the whole crew PAN brings to the pit. However, this gives you an idea of how each crew member brings something unique to keep that firewall running like a finely tuned machine. “Tuned” is the operative word as we recall what Gartner has said about misconfigurations.
The BPA+ tool provides you with a highly detailed report on which security functions are in your pit, and which have been sidelined.
As with the SLR, it will compare your feature adoption rate with that of the average for your industry vertical. That average is ever-changing! The world in general is becoming more security-aware with each new exploit. You must set a cadence and make a habit of running these BPAs.
The “+” in BPA+
For those already familiar with the BPA, let me tell you how PAN took it to the next level.
The BPA told you where you were falling short in leveraging features, but how do you configure them? PAN has now added wizards for assessment failures that will generate the command-line set commands for you to remediate these shortcomings.
“Okay, Scott, so now I have a list of commands, but I am not entirely sure what impact this will have. Can you help me interpret all this to communicate it upwards?” Absolutely! Nexum security professionals, including me, are here to do exactly that.
PAN will be rolling out even more features in the future. The “+” is a fantastic evolution of the BPA we have known and loved.
What does it all mean?
Security hasn’t been a “set it and forget it” technology for a long time. Bad actors are getting more sophisticated faster than end-users are becoming more security-savvy. We, as security professionals, need to be diligent in the continuous improvement and adoption of emerging defensive capabilities.
Nexum and Palo Alto Networks’ SLR and BPA+ tools can help you understand your exposure today and a path to improve your security posture to mitigate risk.
Now go forth, check your calendar, and let’s get something set up.
Check Out More Resources

Juniper EX4000
Nexum’s, Allyn Crowe, breaks down what sets the latest EX4000 series switch apart—powerful PoE, multigig support for next-gen Wi-Fi, and faster performance. With quick boot times and seamless upgrades, it’s a smart choice for future-proofing networks.
Juniper Announces Wi-Fi 7 Access Points
Nexum’s engineering team highlights Juniper’s new Wi-Fi 7 AP47 as a game-changer, offering faster speeds, quad radios, and enhanced IoT capabilities. With dual 10Gbps interfaces and AI-driven Wi-Fi 7 support, these access points are designed for cutting-edge network performance.
AI-Native Now
Join Juniper Networks on June 5th for a LinkedIn Live exclusive discussion on “Leveraging AIOps for Maximum Impact.”